Increased connectivity, high-speed data networks and digitalization have changed the design and operation of vessels and this has involved too new vulnerabilities: Cyber threats are continuously evolving in the shipping industry, and pleasure yachts are not an exception, highlighting growing YachtCyberRisk and the need for Maritime Cybersecurity by design.
Just 15% only of shipowners understand the importance of a cyber-secure vessel upon delivery, and the same percentage of shipyards confirm to have internal resources with the necessary expertise. These are not assumptions, but the results of a recent research conducted by a UK based strategic technology analysis Company. These figures primarily refer to the maritime industry in general, but the yacht market segment is no exception, reinforcing why CyberSecureVessels must be a priority from day one.
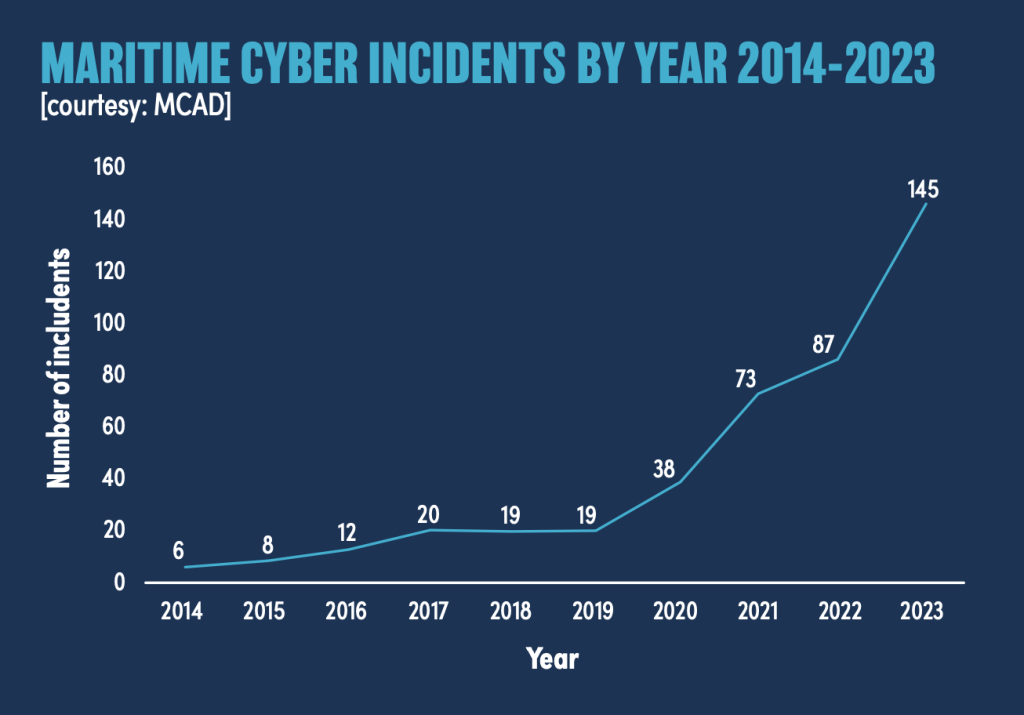
Maritime cyber incidents by year 2014 – 2023
THE PARADIGM SHIFT IN TECHNOLOGY
The increasing digitalisation and interconnection of the maritime industry have enhanced onboard safety, operational efficiency, and environmental sustainability. The total market of digital technology for the maritime industry in general is estimated to reach USD $345 billion by 2030, just five years only from now. These new developments of digital technologies allow a fast data and information exchange and apply to almost any kind of vessels, from pleasure boats to merchant, passenger, and other specialized vessels. Ports and their operations are also an active part of this new interconnected world, which expands the MaritimeCybersecurity perimeter from ship to shore.
INCREADES RISKS
However, there has been an increased risk of cyber threats in parallel to the enhancements, and with a growing in frequency, sophistication, and severity of cyber incidents. In 2023, 14% of marine stakeholders confirmed to paying ransoms, while in 2024 this percentage have dropped, with an average payment under USD $100 K. Shipyards, shipowners and ship managers should prioritize integrating security in their connectivity strategy to build Cyber Secure Vessels that can withstand evolving attack vectors.
This means that cyber security cannot be added at a later stage as an afterthought, in response to threats as soon as they appear. Cybersecurity must be included into every stage of a vessel’s life cycle and integrated from the initial design phase up to the commissioning, operation and refitting, thus taking into consideration an approach based on the entire life cycle of the vessel. Effective cooperation between owners, shipyards and equipment manufacturers becomes mandatory, together with a reliable plan for crew awareness and training, to reduce Yacht Cyber Risk across IT and OT systems.

RULES AND REGULATIONS
To reduce the impact and the consequences of maritime cyber incidents, the international organizations have introduced specific rules and requirements.
· International Maritime Organization (IMO)
IMO have issued 2 documents about cyber security and applicable to all vessels of 500 GT and more:
- The first one is the MSC-FAL-17Circ.3/Rev.2 of June 2022, providing guidelines how to manage cyber risks to safeguard from current and emerging cyber threats to support safe and secure ships operation resilient to cyber risks.
- The other one is the Resolution MSC428 (98) of June 2017 ‘Maritime cyber risks in safety management systems’ implemented in 2021, requiring owners and ship operators to consider overall cyber risks, and to implement cyber security across all levels of their management system, in line with International Safety Management (ISM) Code. These frameworks are core references in MaritimeCybersecurity programs.
· International Association of Classification Societies (IACS)
IACS has published 2 Unified Requirements (URs) for cybersecurity, having effect from 1 July 2024, requesting ship owners, shipyards and system or equipment suppliers to provide cyber security barriers into their systems and vessels. The URs for cyber security include two sets of rules: E26 manages system integration, while UR E27 applies to essential onboard systems. They involve both suppliers and yards and are mandatory for all new buildings contracted after 1 July 2024. Essential systems are computer-based systems designed for main engine control systems, steering control systems, fire detection, communication systems including public address systems, and navigation systems. Compliance with IACSE26E27 is now a competitive and regulatory must-have for CyberSecureVessels.
· Other guidance and standards
Other guidance and standards for marine cyber security have been released, like the “Guideline on Cyber Security on board Ships” issued by ICS, IUMI, BIMCO, OCIMF, INTERTANKO, INTERCARGO, InterManager, WSC and SYBAss. The EU Directive on Network and Information Systems (NIS2), implemented in October 2024, makes mandatory to the EU member states to adopt cyber security strategies and establish competent cyber security structures across their jurisdictions. The directive ensures that operators of essential services, including major ports, shipping companies and even single vessels take appropriate security measures and report serious cyber incidents. For EU operators, NIS2Compliance becomes integral to governance and operational readiness.
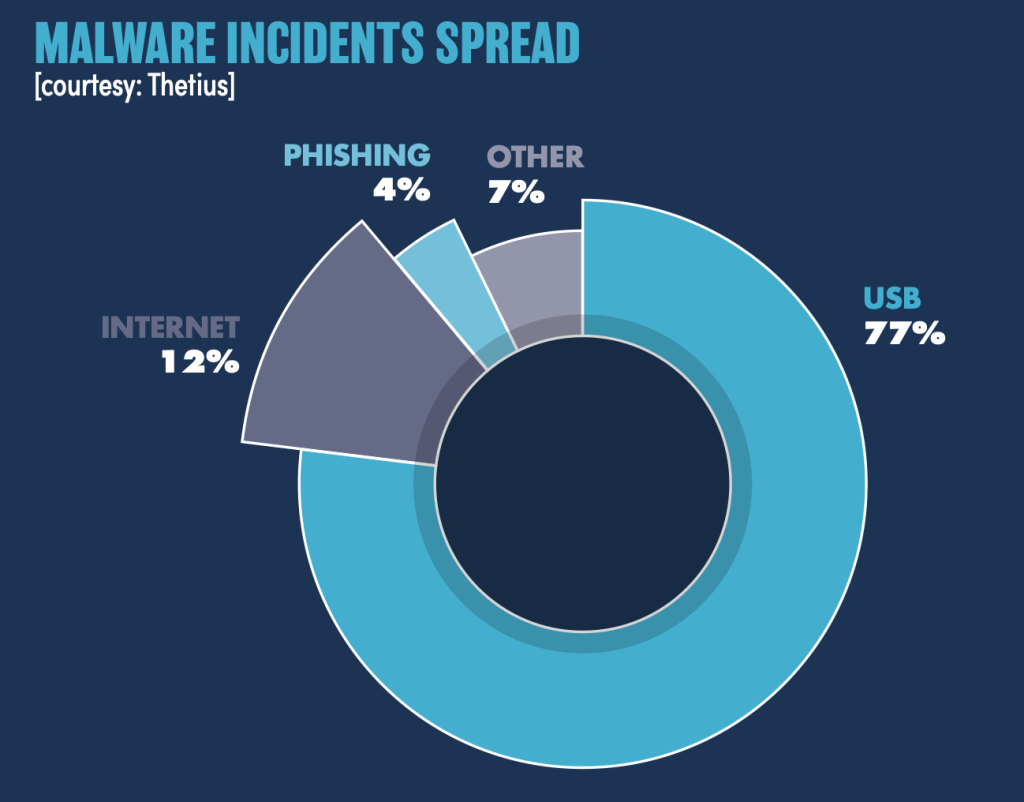
Malware incidents spread
DESIGNING, BUILDING, AND OPERATING A CYBER-SECURE VESSEL
Reports by research institutes about marine cybersecurity measures highlight the need for a lifecycle span approach from the design to daily operation of the vessel. This ensures that potential risks are evaluated and addressed at the beginning of the vessel lifecycle, avoiding costly changes or refitting at a later stage. High-speed data networks and almost instant communications are a common feature that are requested for any kind of pleasure boats, regardless of their size. The new level of connectivity provides more efficient data exchange between ships and shore but widens also the opportunity for cyber criminals to penetrate system vulnerabilities, increasing YachtCyberRisk if controls are not embedded.
SUGGESTIONS
The following are some suggestions of key actions that the main stakeholders should take into consideration to ensure a long-term capability against evolving threats:
- Integrate cybersecurity from the design phase of the vessel and clearly define responsibilities. Shipowners and management companies should consider the support of specialized companies or classification societies as consultant during this phase to ensure MaritimeCybersecurity best practices.
- Establish a minimum-security architecture specification for all systems to be interconnected. This approach, known as Code of Connection, has proven to work well in other industry and defence sectors and helps create CyberSecureVessels by design.
- Require the adoption of international standards such as UR26 and UR27 that provide clear and valuable specifications and can be adapted to any connected vessel. Consider also best practices from IT and power-generation industries, aligning engineering and documentation with IACSE26E27 requirements.
- Select secure-by-design equipment where possible, and promote cooperation, transparency and data sharing between all stakeholders to reduce YachtCyberRisk and improve incident response.
- Assess cybersecurity during the delivery of the vessel from shipyard and implement periodic simulated cyber-attacks and drills during the operation, to test the skill of the crew and shore organization, supporting continuous NIS2Compliance where applicable.

THE REFITTING DILEMMA
A more complex issue when dealing with cybersecurity of existing boats or vessels, equipped with legacy systems. Fleet management companies should approach this problem with the same strategy used for new buildings, while owners or managers of single vessels should consider the following roadmap. In retrofit scenarios, focusing on MaritimeCybersecurity baselines, segmentation and secure remote access is key to upgrading legacy assets into CyberSecureVessels with controlled YachtCyberRisk and, for EU operators, alignment to NIS2Compliance.
| Step | Action |
| Assessment | Mapping of connected systems, risk analysis (vulnerability and threats) |
| Segmentation | Logic or physical separation of networks, firewalls, data diodes |
| Hardening | Update firmware and software (where possible), and disconnect unused ports |
| Compensatory measures for non-upgradeable systems | Physical isolation of legacy systems, security gateways, data traffic monitoring |
| Access control | Implement a strong 2FA (two factors authentication), limit remote access possibilities, logging of network access |
| Crew training | Awareness, procedures, simulation, and drills of cyber incidents |
| Incident Response Plan (IRP) | Roles and responsibilities, procedures, data recovery, notification of cyber incidents |
| Continuous monitoring and improvement | Logs, updates, and periodic tests |
HUMAN FACTORS
Crew members are trained to operate the vessel, not handle complex IT systems, but they’re often left with that responsibility. They are typically unprepared for real cyber threats, emphasizing a gap between training and practical application.
A survey by a consulting firm discovered that 93% of the onboard operators feel unprepared to manage the current cybersecurity challenge and 60% feel they lack the expertise and tools to address cybersecurity issues. Feedback from actual cases has shown that sometimes there were events onboard vessels that were real cyber incidents, but the crew did not even recognize or identify them as such. Malware incidents are primarily due to removable media like USBs (or alien laptops), representing 77% of total cases, followed by 12% due to internet downloads.
The expectation that ship crews must be able to manage complex issues of cybersecurity is unrealistic. As an example, we do not expect that a health-care specialist in a hospital is capable of verifying the cyber security of a Magnetic Resonance Imaging scanner or of providing an incident response. Crew members are often unprepared for real cases because of desktop training only, usually based on a checklist requirement, unlikely helpful when a real incident occurs. More effective, instead, is to create a cybersecurity mindset among the crew, accompanied by real-time support during cyber incidents.
CONCLUSIONS
Understanding of cybersecurity risks, sharing of responsibilities, cooperation between owners, shipyards and makers, support by Class Societies are the keys to an effective risk management and operational security over the life cycle of the vessel. Crew training and awareness are the same important because, as the renowned ‘security guru’ Bruce Schneier said, “Amateurs hack systems, professionals hack people”.